F
ForgottenSeer 85179
@Andy Ful i guess this is interesting for you:
Microsoft Defender Antivirus Attack Surface Reduction Rules Bypasses – Thalpius
Microsoft Defender Antivirus Attack Surface Reduction Rules Bypasses – Thalpius
Thanks, I did not know this article.@Andy Ful i guess this is interesting for you:
Microsoft Defender Antivirus Attack Surface Reduction Rules Bypasses – Thalpius
Managing script false positive detections (antimalware, AMSI, ASR).
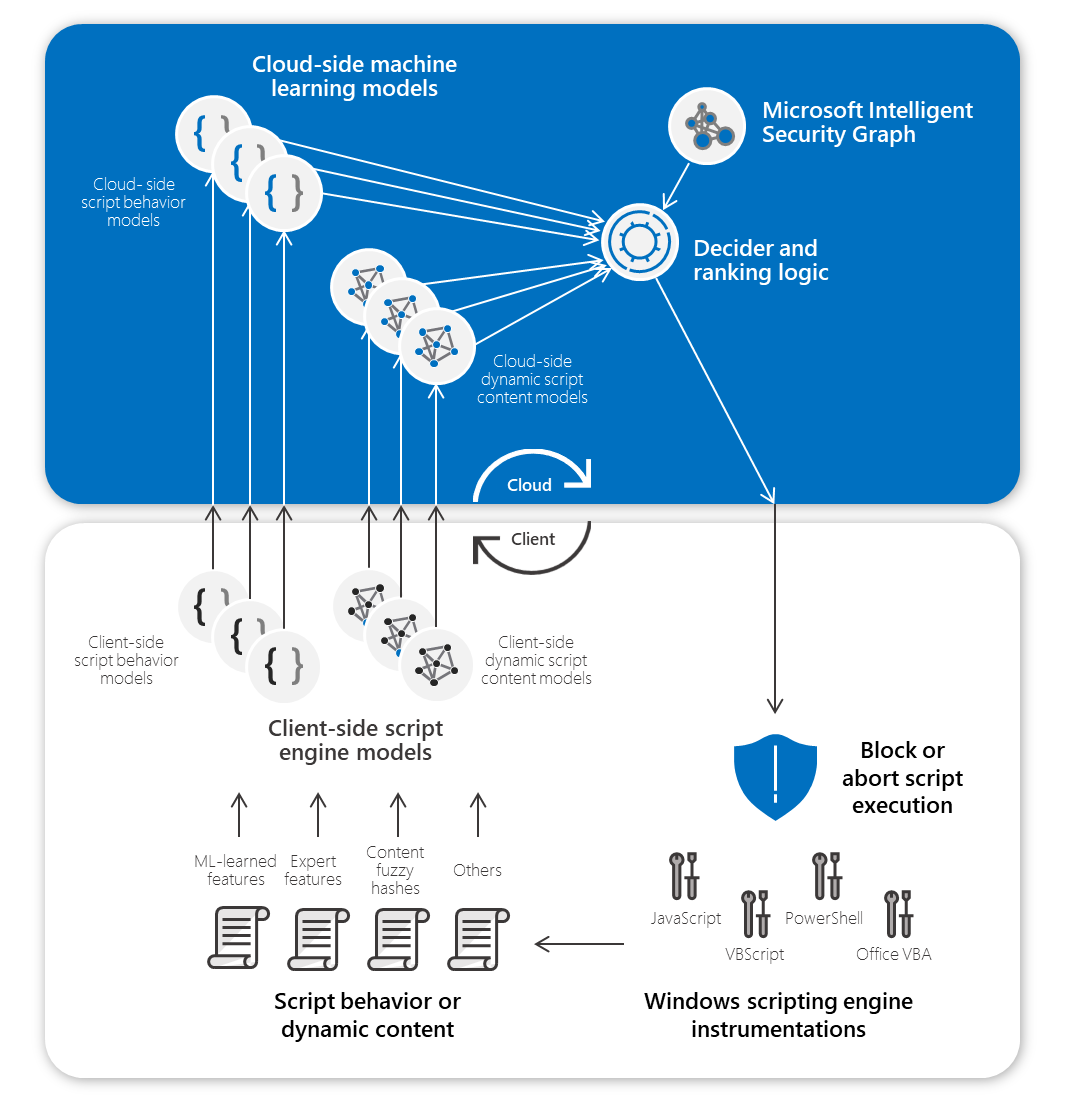
Defender can detect/block scripts by several different security layers, for example:
False detections from points 1, 2, and 3 can be separately excluded via Security Center. The false positive ASR blocks can be excluded by using PowerShell, GPO, or ConfigureDefender.
- Antimalware (pre-execution) detection.
- AMSI-paired machine models (pre-execution) detection.
- AMSI-paired machine models (post-execution) detection.
- ASR rules.
AMSI-based detections are similar to other behavior-based detections. AMSI is used to supply machine learning models with code in clear text to avoid string obfuscation.
In the pre-execution case, the code is scanned and the script is blocked if recognized as malicious by behavior models.
In the post-execution case, the code execution is monitored and analyzed by dynamic behavior models. The execution is interrupted when the suspicious actions exceed the detection threshold. Although the scripting engine alerts can suggest that the particular script code is blocked (like "Wshshell.run"), it does not mean that after excluding this detection, the blocked script code (like "Wshshell.run") will be allowed for other scripts. It is an important feature because otherwise, such exclusions would decrease the protection.

 malwaretips.com
malwaretips.com


| Type | Attribute |
|---|---|
| Machine attributes | OS version Processor Security settings |
| Dynamic and contextual attributes | Process and installation ProcessName ParentProcess TriggeringSignature TriggeringFile Download IP and url HashedFullPath Vpath RealPath Parent/child relationships Behavioral Connection IPs System changes API calls Process injection Locale Locale setting Geographical location |
| Static file attributes | Partial and full hashes ClusterHash Crc16 Ctph ExtendedKcrcs ImpHash Kcrc3n Lshash LsHashs PartialCrc1 PartialCrc2 PartialCrc3 Sha1 Sha256 File properties FileName FileSize Signer information AuthentiCodeHash Issuer IssuerHash Publisher Signer SignerHash |

Cloud Protection Levels
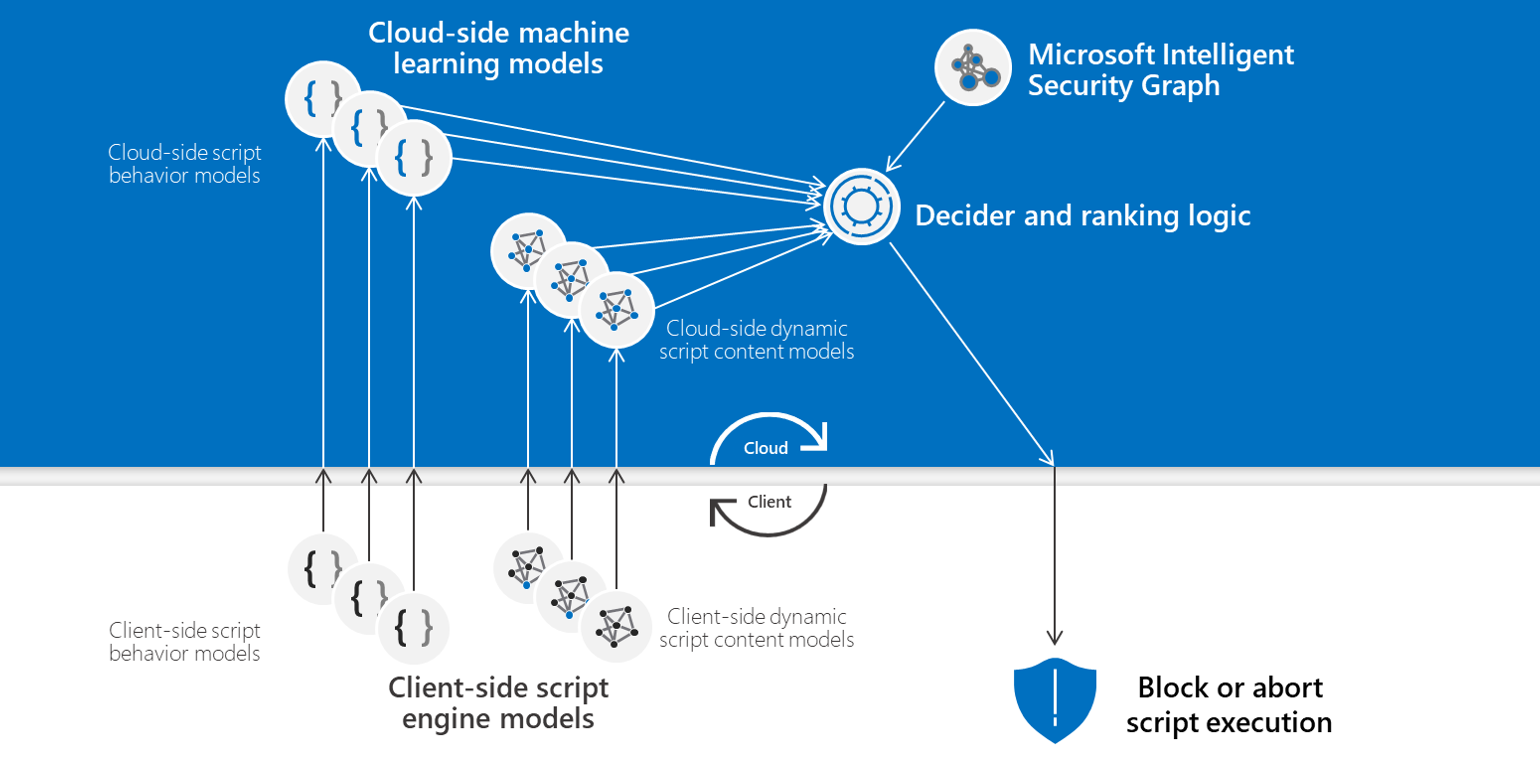
There is a lot of misunderstanding about how Cloud delivered protection works. Here is a diagram from the Microsoft documentation:

Cloud protection and sample submission at Microsoft Defender Antivirus - Microsoft Defender for Endpoint
Learn about cloud-delivered protection and Microsoft Defender Antivirusdocs.microsoft.com
View attachment 266439
The red arrow shows the moment when Cloud protection level "Zero tolerance" (Block setting in ConfigureDefender) will block the unknown file. The decision is made in the cloud after the analysis of telemetry (file metadata check). The file is not uploaded to the cloud. Some files can still infect the system if they are not recognized as suspicious by local protection layers - they are not checked by the cloud backend even on execution. Only when the file has got MOTW (file downloaded via web browser) it is obligatory checked by the cloud backend via BASF.
The blue arrow shows the moment when the High and High+ (Highest setting in ConfigureDefender) Cloud protection levels are important. They work after uploading the file to the cloud. In this case, the analysis can last longer but we have a lower rate of false positives.
...

 blog.ahasayen.com
blog.ahasayen.com
Cloud-Delivered Protection Blocking Levels
When the cloud returns a verdict for a submitted file (sample) from the client, you can configure your tolerance-to-risk ratio by configuring blocks level in Microsoft Defender Antivirus:
- Blocking level = High: applies a strong level of detection while optimizing client performance (greater chance of false positives).
- Blocking level = High+: applies additional protection measures (may impact client performance and increase risk of false positives).
- Zero tolerance blocks all unknown executables.